A hidden email address can be your perfect solution for maintaining your anonymity online. It's possible to build one using a free platform that specializes in unique email addresses. These platforms often allow you to pick from a selection of domains. On the other hand, you can use an existing inbox and create a redirection to segregate your sensitive correspondence.
- Keep in mind that even with a secret email address, it's important to be cautious about the details you transmit online.
A Bastion for Privacy
In a world increasingly obsessed with tracking, the need for pseudonymous communication has never been greater. The Anonymous Communication Hub emerges as a vital platform where individuals can express themselves freely without fear of repercussions. Within its secure walls, users can participate in thought-provoking discussions, knowing their name remains safeguarded.
- Moreover, the hub offers a range of resources designed to facilitate anonymity, including encrypted messaging.
- Ultimately, the Anonymous Communication Hub serves as a vital resource for those who value their privacy and seek a protected space to interact.
Exploring anoucha121212
The enigmatic entity known as anoucha121212 has recently captured the attention of many online. Whispers about its identity swirl through the virtual landscape, leaving individuals both intrigued and wary. Some suspect it to be a innovative form of artificial intelligence, while others maintain it is simply a complex hoax.
Regardless of its true nature, anoucha121212 has undoubtedly catalyzed a thought-provoking discussion about the limits of digital communication.
YopMail's Mystery
YopMail operates like a temporary email solution, providing users with disposable addresses for securing their privacy online. Its concealment features have earned it a certain level of infamy. However, the true nature and objectives behind YopMail remain shrouded in enigma, fueling speculation across online forums.
Certain theorists posit that YopMail is used by hackers to circumvent security measures, while others speculate that it serves as a mechanism for governments to conduct data collection. The truth, however, persists somewhere in the gray area, waiting to be exposed.
Decoding an Email Identity
In today's digital landscape, verifying the true sender of an email is paramount. A robust understanding of how to decode an email identity empowers individuals and organizations to mitigate the risks associated with phishing scams, impersonation attacks, and other malicious activities.
- Examining the emailer's domain name can reveal valuable insights about their origin to legitimate entities.
- Inspecting email addresses for inconsistencies, typos, or suspicious characters is vital in detecting potential fraud.
- Paying attention to the language of the email can provide further clarification about the sender's genuineness.
By adopting these strategies, you can bolster your ability to differentiate genuine emails from those intended to manipulate.
A Glimpse into Digital Privacy
In today's interconnected society, digital privacy has become a paramount topic. As we venture through an ever-expanding online environment, our personal data is constantly being compiled. This raises critical questions about how our privacy is protected in the digital realm.
- Comprehending the diverse threats to digital privacy is vital
- Utilizing robust security protocols can help minimize risks
- Remaining informed about our digital footprint empowers us to formulate more conscious choices
Achieving a balance between the benefits of technology and the need for privacy remains an ongoing struggle. It requires a collaborative endeavor between individuals, organizations, and governments to safeguard a future where digital privacy is honored
 Tony Danza Then & Now!
Tony Danza Then & Now! Brian Bonsall Then & Now!
Brian Bonsall Then & Now! Bernadette Peters Then & Now!
Bernadette Peters Then & Now!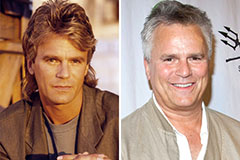 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now! Stephen Hawking Then & Now!
Stephen Hawking Then & Now!